In a landmark case before the UK High Court, the alleged theft of 2,323 Bitcoin (BTC), valued at approximately $176 million at the time of the claim, has brought to light a critical, often overlooked vulnerability in digital asset security: the human element and physical surveillance. Far from involving sophisticated hacking or malicious software, the dispute centers on allegations of a seed phrase being secretly recorded, effectively bypassing the technical safeguards of a hardware wallet and challenging conventional notions of crypto security. This high-profile case underscores that while cryptographic strength remains paramount, the real weak link often lies in the physical environment, personal conduct, and the intricacies of human relationships.
The Case in Detail: A Human Element of Vulnerability
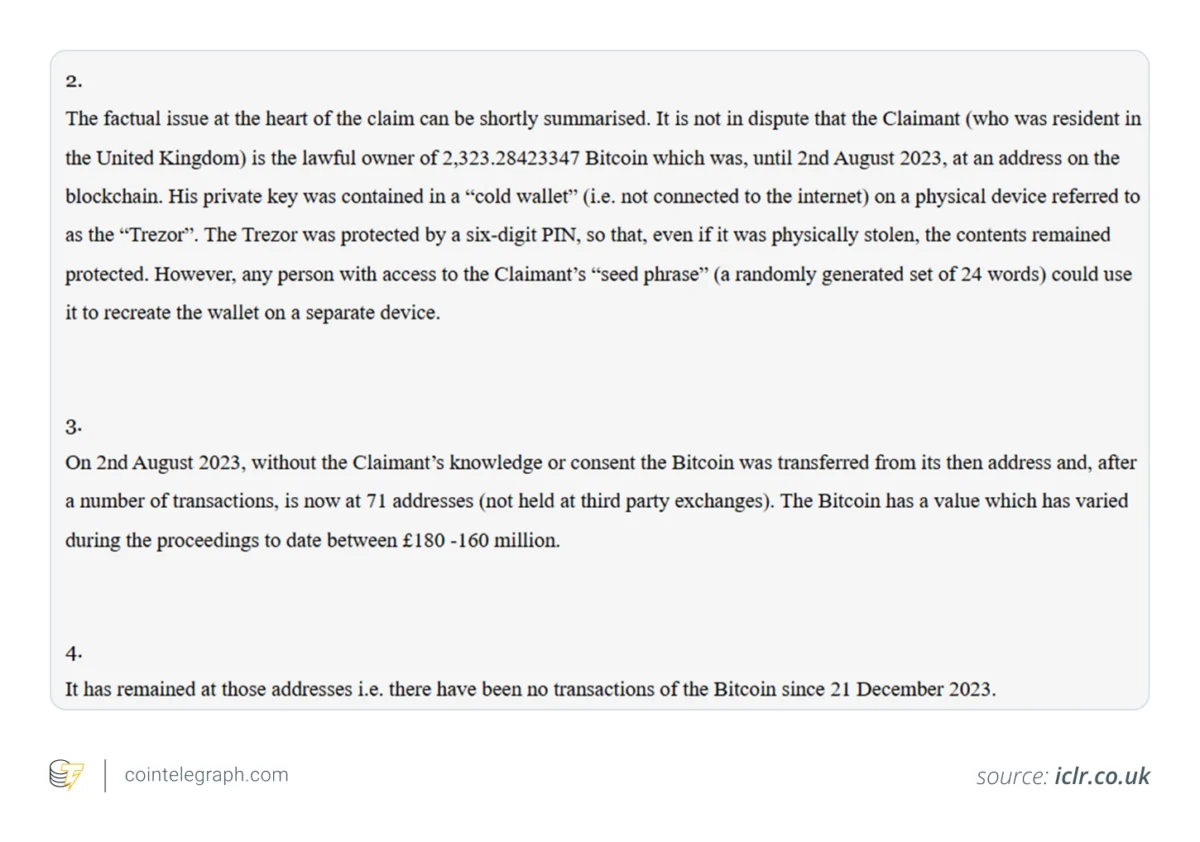
The proceedings before the UK High Court revolve around Ping Fai Yuen, who claims his estranged wife, Fun Yung Li, and her sister illicitly gained access to his substantial Bitcoin holdings. The core of the accusation is that the theft did not involve a breach of encryption or a sophisticated cyberattack, but rather the clandestine exposure of his wallet’s recovery information – specifically, his seed phrase. This phrase, typically a sequence of 12 to 24 words, serves as the ultimate backup and master key to a cryptocurrency wallet, irrespective of the physical device used for storage.
The assets were reportedly held in a hardware wallet, a device widely considered a gold standard for self-custody due to its design to keep private keys completely offline and shielded from remote threats like malware and phishing. Hardware wallets isolate private keys from internet-connected devices, making them highly resistant to digital intrusions. However, as this case starkly illustrates, their efficacy is predicated on the absolute secrecy of the seed phrase. Once this crucial piece of information is compromised, the physical security of the hardware wallet becomes irrelevant, as the funds can be restored and controlled from any compatible device using the exposed seed phrase. Court documents suggest the alleged theft required no technical hacking prowess, only the discovery of this single point of failure.
The estimated value of the stolen Bitcoin, around $176 million, places this incident among the most significant non-technical crypto thefts publicly litigated. To put this into context, at the time of the alleged transfer in December 2023, Bitcoin’s price fluctuated, making such a sum a substantial target for any form of illicit acquisition. This incident serves as a potent reminder that the robust cryptography underpinning blockchain technology is only as secure as the weakest link in its implementation, which, in many cases, can be the user’s operational security in the physical world.
Chronology of Allegations and Discovery
While the full timeline of events leading to the alleged theft and subsequent legal action is still unfolding in court, the available information paints a picture of a carefully orchestrated non-digital intrusion. The allegations describe events that lean heavily towards surveillance rather than digital hacking.
The crucial alleged event appears to be the covert recording of Ping Fai Yuen’s recovery information. While the exact date of this recording is not specified in public documents, it must have preceded the alleged transfer of funds. According to the claimant, Fun Yung Li and her sister gained access to the seed phrase through surreptitious means, potentially involving hidden cameras or audio recording devices within a shared or accessible environment. This suggests a period of observation and planning, rather than an opportunistic digital attack.
The actual movement of the Bitcoin funds occurred on or around December 21, 2023. Court documents indicate that a substantial amount of 2,323 BTC was transferred from Yuen’s control. Crucially, no additional movements have appeared on the blockchain for these specific assets since that date, indicating that the funds have remained inactive following the reported transfer. This inactivity simplifies the tracing process for blockchain forensics but complicates recovery if the funds have been moved into multiple wallets or exchanges.
Following the discovery of the alleged theft, Yuen initiated legal proceedings in the UK High Court. Authorities, likely spurred by the court’s intervention or a separate criminal complaint, are reported to have confiscated devices and cold wallets as part of the ongoing inquiry. These seizures would be critical for forensic analysis, potentially confirming the alleged transfer and identifying the destination of the stolen assets. The legal proceedings are still in their early stages, with the High Court having issued an interim judgment, signaling a strong likelihood of the claimant’s success based on the initial evidence.
The Indispensable Seed Phrase: Master Key to Digital Wealth
At the heart of this case lies the seed phrase, a seemingly innocuous string of words that holds the key to an entire cryptocurrency wallet. For those unfamiliar with the mechanics of self-custody, understanding the seed phrase’s critical role is paramount. A seed phrase, often adhering to the BIP-39 standard, is a mnemonic representation of a master private key. This master key, in turn, deterministically generates all the individual private keys for the wallet’s addresses. This hierarchical deterministic (HD) wallet structure means that a single seed phrase can recover an entire wallet, along with all its associated addresses and funds, across any compatible wallet software or hardware.
Hardware wallets are designed to protect private keys by keeping them isolated from online environments. However, the seed phrase acts as a full backup of the entire wallet, including all the private keys it contains. This means that anyone who obtains the seed phrase can bypass the physical security of the hardware wallet entirely. They can simply input the seed phrase into a new hardware wallet or a software wallet on any device and instantly gain full control over all the associated funds. The physical device itself loses all relevance once its corresponding seed phrase is compromised.
The implications of seed phrase exposure are profound and often irreversible. With the seed phrase, an unauthorized individual can:
- Restore the wallet on a new device.
- Access all funds stored in the wallet.
- Initiate transactions, sending the crypto assets to new addresses.
- Change security settings or add new addresses.
- Effectively drain the entire wallet’s contents, rendering the original owner powerless.
This fundamental principle underscores why the seed phrase is often considered the "master key" or "root password" to one’s digital wealth. Unlike traditional banking where a compromised password might lead to a bank freezing an account, blockchain transactions are immutable and irreversible. Once funds are transferred by someone with the seed phrase, reclaiming them is a complex legal and forensic challenge, rather than a simple reversal.
Beyond Code: The Rise of Side-Channel Attacks
What distinguishes this particular case and elevates its significance is the alleged method of compromise. In an ecosystem frequently battling sophisticated phishing campaigns, malware, and exchange hacks, this incident highlights a seldom-discussed but increasingly relevant threat: side-channel exposure, particularly through physical surveillance. Rather than relying on digital intrusion techniques, the allegations center on visual or audio capture of the seed phrase, possibly through a hidden camera, covert recording, or even simple "shoulder surfing."
Side-channel attacks, in the context of crypto security, exploit information leakage from the physical implementation of a system rather than weaknesses in the cryptographic algorithms themselves. When seed phrases are generated, written down, spoken aloud during confirmation, or even typed into a temporary interface (though less common for hardware wallets), they become vulnerable to physical observation.
This vulnerability is exacerbated by the ubiquitous presence of smart devices in modern environments. Homes and offices are increasingly equipped with smart speakers, security cameras, and other IoT devices that can be compromised or repurposed for covert surveillance. If any of these moments are watched or recorded:

- The entire security model of self-custody collapses.
- The hardware wallet, despite its robust design, becomes defenseless.
- The private keys, intended to be offline, are effectively "leaked" through human interaction.
This method of compromise presents a unique challenge because it cannot be directly mitigated by traditional cybersecurity measures like antivirus software, firewalls, or secure network protocols. Instead, it demands a heightened awareness of physical security, privacy in personal spaces, and vigilance regarding one’s surroundings. The "Did you know?" insight from the original article that "hidden cameras, not hackers, have been the weakest link in crypto security" in past cases, powerfully reinforces this point. Physical surveillance, often underestimated, is quietly emerging as a significant threat to self-custodied digital assets, especially for high-net-worth individuals who might be targets of sophisticated, real-world social engineering or personal attacks.
UK High Court’s Early Intervention and Legal Precedent
The matter came before the UK High Court, where Justice Cotter examined the evidence presented for an interim injunction and asset freezing order. While this does not constitute a final decision on the merits of the case, the judge indicated that the claimant had demonstrated a "very high probability of success" at trial. This preliminary stance is significant, as it suggests the court found compelling evidence supporting the allegations of theft via seed phrase compromise.
Among the elements considered by Justice Cotter were:
- CCTV footage: This likely provided visual evidence corroborating the alleged surveillance or access to the claimant’s private space where the seed phrase might have been exposed.
- Audio recordings: These could have captured conversations or sounds related to the seed phrase’s generation or retrieval, further substantiating the claim of covert recording.
- Alleged admissions: Any statements or confessions made by the accused parties, if presented as evidence, would carry substantial weight in court.
- Blockchain transaction data: The immutable record of the Bitcoin transfer itself would serve as concrete evidence that the assets had been moved from the claimant’s control.
The court also stressed the need for swift action, citing both security concerns and Bitcoin’s inherent price fluctuations. The volatile nature of cryptocurrency markets means that delays in freezing or recovering assets can lead to significant changes in their fiat value, potentially impacting the claimant’s ability to recover their full losses. This highlights the challenges that traditional legal systems face in adapting to the unique characteristics of digital assets, where speed and global coordination are often critical.
The court’s willingness to grant an interim order based on physical surveillance evidence sets an important precedent. It signals that legal frameworks are evolving to address non-traditional forms of digital asset theft, moving beyond purely cybercrime definitions. This case could influence how courts worldwide approach similar disputes, particularly those involving marital or familial relationships where trust and access to personal spaces are often central. It reinforces the idea that legal recourse is available even when the "hack" is analog rather than digital.
Strategic Asset Distribution and Dusting Concerns
A notable detail in the claimant’s legal submission is that the stolen Bitcoin was allegedly distributed across 71 separate wallet addresses. This action carries several implications that can complicate the asset recovery process:
- Obfuscation and Complexity: Spreading funds across numerous addresses can be a strategic move to make tracing and consolidating the assets more difficult for the victim and law enforcement. While the blockchain is transparent, tracking 71 separate movements and then identifying the ultimate destination of each fragment requires considerable forensic effort.
- Preparation for Mixing Services: Distributing funds into many smaller chunks can be a precursor to using mixing services (e.g., CoinJoin) or decentralized exchanges (DEXs), which aim to break the chain of custody and further anonymize transactions. If the funds are scattered and then mixed, recovery becomes significantly more challenging.
- Avoiding Large-Scale Seizure: Holding large amounts in a single address makes it a prime target for a single seizure order. By fragmenting the holdings, the alleged thieves might have aimed to mitigate the risk of a complete asset freeze, requiring multiple, more complex legal actions.
- Pseudo-anonymity: While Bitcoin transactions are public, linking specific addresses to individuals relies on external information. Distributing funds among many addresses can make it harder for blockchain analysis firms to cluster these addresses under a single entity without additional data.
Although the blockchain’s inherent transparency allows movements to be traced, spreading the funds across many addresses adds layers of complexity and time to any recovery process. This deliberate fragmentation often indicates a sophisticated attempt to evade detection and hinder asset retrieval.
Furthermore, the claimant also expressed concern about a possible "dusting attack" on the involved addresses. Dusting refers to the act of sending tiny amounts of cryptocurrency (known as "dust") to a large number of wallet addresses. The purpose of a dusting attack is typically to:
- De-anonymize Wallets: By sending dust to many addresses, an attacker hopes to link them together, especially if those addresses subsequently interact with centralized exchanges where KYC (Know Your Customer) information is collected. This can help identify the real-world identity of the wallet owner.
- Track User Activity: Once a wallet is "dusted," its subsequent transactions can be monitored. If the dust moves, it provides insights into the wallet’s activity and potentially its owner’s broader crypto holdings.
- Phishing or Social Engineering: In some cases, dusting can be a precursor to targeted phishing attempts, where the attacker uses the knowledge gained from de-anonymization to craft more convincing scams.
If the compromised wallet addresses become public through court filings or other means, they can attract additional scrutiny and become targets for such privacy-invasive attacks, even if no further legitimate activity occurs on those specific addresses. This adds another layer of concern for the victim, as their financial privacy could be further eroded.
Broader Implications for Crypto Custody and Security Paradigms
While this case remains a private legal dispute between estranged family members, it serves as a powerful and pertinent case study in the broader risks associated with crypto custody. It challenges the common perception that robust cryptographic solutions inherently guarantee security, revealing that the perimeter of protection extends far beyond digital safeguards.
This incident demonstrates that:
- Hardware wallets are not foolproof: Their security is dependent on the secrecy of the seed phrase, which can be compromised through non-technical means. A hardware wallet is only as secure as the environment in which its seed phrase is generated, stored, and used.
- Security is multi-faceted: It involves not just technological defenses but also stringent operational security practices, a secure physical environment, and careful consideration of personal trust and relationships. The human element, including vigilance and discretion, plays an undeniable role.
- The "weakest link" is often human: Sophisticated social engineering, coercion, or, as alleged here, covert surveillance, can bypass even the strongest cryptographic protections by targeting the point where humans interact with their digital assets.
- Trust and relationships are critical vulnerabilities: In cases involving close personal connections, the implicit trust can be exploited, making individuals susceptible to attacks that would be far less effective from an unknown third party. This adds a layer of complexity to risk assessment.
Above all, this case shows that crypto security involves far more than just devices and code; it relies heavily on environment, conduct, trust, and relationships. It compels a re-evaluation of personal security protocols for anyone holding significant digital assets in self-custody. The traditional threat model, often focused on external hackers, must now fully incorporate internal threats, physical breaches, and the inherent vulnerabilities of human interaction with sensitive information. This evolving understanding of risk will undoubtedly shape future security practices and legal considerations in the burgeoning world of digital finance.
Fortifying Digital Assets: Essential Security Lessons
The UK High Court case offers invaluable lessons for anyone engaging in self-custody of cryptocurrency. It reinforces several straightforward yet crucial guidelines, alongside more sophisticated arrangements, to mitigate the risk of compromise:
- Absolute Secrecy of the Seed Phrase: The seed phrase must be treated as the most valuable and sensitive piece of information related to your digital assets. Never store it digitally (e.g., on a computer, phone, or cloud service). It should ideally be written down on paper or, for enhanced durability, etched onto metal.
- Secure, Offline Storage: The physical copy of your seed phrase must be stored in a highly secure, private location. This means a fireproof safe, a bank vault, or other secure containers that are inaccessible to unauthorized individuals. Geographically dispersed backups (e.g., splitting the seed phrase and storing parts in different secure locations) can provide resilience against localized disasters or single points of physical compromise.
- Vigilance Against Physical Surveillance: Be acutely aware of your surroundings, especially when setting up or recovering a wallet. Ensure no hidden cameras, audio recorders, or prying eyes can observe you. This includes being mindful of smart devices in your home or office that could be compromised. Performing sensitive operations in a private, controlled environment is paramount.
- Strong Authentication on Hardware Wallets: Utilize all available security features of your hardware wallet, including strong PINs and passphrases. Change default PINs immediately. Some wallets now offer "decoy wallets" or "plausible deniability" features, allowing users to set up a secondary PIN that reveals a smaller, less valuable wallet if coerced or under surveillance. This can buy time or deter attackers.
- Multi-Factor Security for Associated Accounts: Ensure any accounts linked to your crypto activities (e.g., email, exchange accounts) are secured with strong, unique passwords and robust two-factor authentication (2FA), preferably using hardware-based keys (like YubiKey) rather than SMS or authenticator apps.
- Advanced Security Setups: For individuals holding significant amounts of crypto, more sophisticated arrangements are highly recommended:
- Additional Passphrases (BIP-39 Passphrase): This acts as a "25th word" that, when added to the standard 12 or 24-word seed phrase, creates a completely new, separate wallet. Without this passphrase, the seed phrase alone will only recover a different, empty wallet. This offers plausible deniability and an extra layer of protection against a compromised seed phrase.
- Split Backups (Shamir’s Secret Sharing): Instead of having a single copy of the seed phrase, this cryptographic technique splits it into multiple unique shares, where a predefined number of shares (e.g., 3 out of 5) are required to reconstruct the original. This eliminates a single point of failure and makes physical compromise much harder.
- Multisignature (Multisig) Setups: This requires multiple private keys (held by different individuals or on different devices) to authorize a transaction. For instance, a 2-of-3 multisig wallet would need any two out of three designated keys to sign off on a transaction. This is ideal for shared funds, organizational treasuries, or individuals who want to distribute control to mitigate the risk of a single key compromise or coercion.
Each of these methods is designed to reduce reliance on a single vulnerable element and distribute risk, creating a more robust defense against both technical and non-technical threats. The UK High Court case serves as a stark reminder that in the realm of digital assets, comprehensive security requires a holistic approach that considers every vector of attack, from the most advanced cyber exploits to the simplest forms of human deception and physical intrusion. The responsibility for securing one’s digital wealth ultimately rests on a foundation of continuous vigilance and disciplined security practices.
This article does not contain investment advice or recommendations. Every investment and trading move involves risk, and readers should conduct their own research when making a decision. While we strive to provide accurate and timely information, Cointelegraph does not guarantee the accuracy, completeness, or reliability of any information in this article. This article may contain forward-looking statements that are subject to risks and uncertainties. Cointelegraph will not be liable for any loss or damage arising from your reliance on this information.