A stablecoin designed to maintain parity with the US dollar, Resolv USR (USR), has dramatically lost its peg following a sophisticated exploit that allowed an attacker to illicitly mint millions of unbacked tokens. The incident, which unfolded rapidly on Sunday, has sent ripples through the crypto community, highlighting persistent vulnerabilities within decentralized finance (DeFi) protocols and the critical importance of robust smart contract security. Resolv Labs, the project behind the stablecoin, has confirmed the breach and has temporarily halted all protocol functions in an urgent bid to prevent further damage and initiate recovery efforts.
The exploit saw an attacker create approximately 80 million USR tokens with minimal collateral, subsequently cashing out a significant portion, leading to a precipitous decline in the stablecoin’s value. On-chain data and analyses from crypto security firms paint a grim picture of a "textbook DeFi hack cashout," which experts estimate yielded the perpetrator around $25 million from the chaotic market reaction. The incident underscores the inherent risks associated with stablecoins, particularly those with complex minting mechanisms, and reignites debates surrounding the stability and trustworthiness of pegged digital assets in the broader cryptocurrency landscape.
Understanding Stablecoins and Resolv USR’s Role
To fully grasp the gravity of the Resolv USR depeg, it is essential to understand the fundamental role and mechanics of stablecoins. Stablecoins are a crucial component of the cryptocurrency ecosystem, designed to bridge the volatile world of digital assets with the stability of traditional fiat currencies like the US dollar. They aim to maintain a constant value, typically $1, making them ideal for trading, lending, and as a store of value without the drastic price swings characteristic of Bitcoin or Ethereum.
There are primarily three types of stablecoins:
- Fiat-backed stablecoins: These are collateralized by traditional assets, such as US dollars, held in bank accounts. Examples include Tether (USDT) and USD Coin (USDC), which are audited regularly to prove their reserves.
- Crypto-backed stablecoins: These are over-collateralized by other cryptocurrencies. MakerDAO’s DAI is a prominent example, backed by a basket of digital assets locked in smart contracts.
- Algorithmic stablecoins: These maintain their peg through automated smart contracts that adjust supply and demand, often involving a secondary volatile token. The infamous collapse of TerraUSD (UST) in May 2022 served as a stark warning about the inherent fragility of some algorithmic designs.
While the exact technical specifications of Resolv USR’s pegging mechanism were not fully detailed in initial reports, the nature of the exploit—involving the deposit of USDC to mint USR—suggests a form of crypto-backed or hybrid model. Such systems typically rely on smart contracts to ensure that every newly minted stablecoin is adequately collateralized, preventing the creation of unbacked tokens that would dilute value and break the peg. Resolv Labs positioned itself as a crypto project, likely operating within the decentralized finance space, offering various services where USR would function as a stable medium of exchange or a foundational asset for yield generation. The integrity of USR was therefore paramount to the entire Resolv ecosystem, making this exploit particularly damaging.

A Chronology of Exploitation and Collapse
The sequence of events leading to USR’s depeg unfolded rapidly, demonstrating the speed at which exploits can be executed and their devastating impact can propagate across decentralized protocols.
- Sunday Morning (UTC): The first signs of trouble emerged on Sunday morning. On-chain data, meticulously tracked by independent analysts, revealed suspicious activity within the Resolv USR contract.
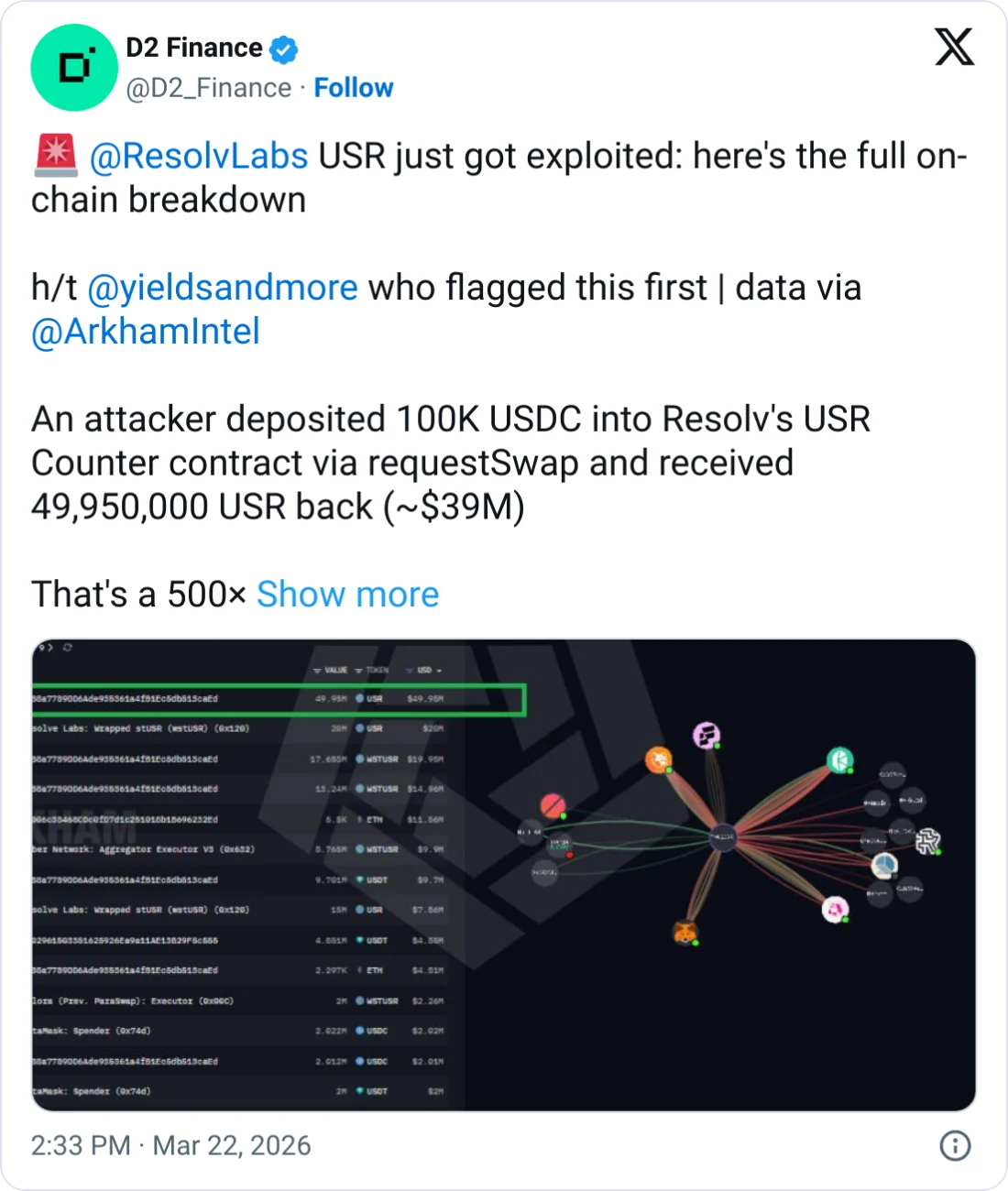
- Initial Minting Spree: An attacker initiated a transaction, depositing a relatively modest sum of approximately $100,000 worth of USDC. Crucially, instead of receiving an equivalent amount of USR, the exploiter was able to mint an astonishing 50 million unbacked Resolv USR tokens. This disproportionate minting immediately signaled a severe vulnerability in the stablecoin’s smart contract or its associated oracle system. The transaction, visible on block explorers like Etherscan, became the primary evidence of the exploit’s initiation.
- Further Token Generation: Shortly after the initial mint, the crypto security firm PeckShield, known for its rapid incident response and on-chain forensics, reported that the attacker was able to mint an additional 30 million USR tokens. This second wave of minting further flooded the market with unbacked assets, exacerbating the impending crisis.
- Market Alerts and Price Crash: The anomaly did not go unnoticed. Crypto Twitter account "yieldsandmore" was among the first to publicly alert the community, posting on X (formerly Twitter) that USR had crashed, citing the on-chain evidence of the attacker’s illicit minting. Simultaneously, the increased supply of unbacked USR, combined with the attacker’s immediate efforts to liquidate these tokens, caused the stablecoin’s price to plummet.
- Resolv Labs Responds: In the wake of the unfolding crisis, Resolv Labs officially acknowledged the exploit via a post on its X account. The team stated, "Resolv Labs has experienced an exploit that allowed an attacker to mint 50 million unbacked Resolv USR (USR). The team has currently paused all the protocol functions to prevent further malicious actions and is actively working on recovery." This critical step, while necessary to staunch the bleeding, effectively froze the protocol, preventing legitimate transactions and locking user funds, at least temporarily.
- Attacker’s "Textbook" Cash-Out: As the price of USR spiraled downwards, the attacker executed a rapid and aggressive liquidation strategy. According to analysis from crypto fund D2 Finance, the minted USR was swiftly moved across multiple crypto protocols. The tokens were swapped for more established and liquid stablecoins, USDC and USDt (USDT), before being "aggressively" converted into Ether (ETH). D2 Finance characterized this as a "textbook DeFi hack cashout running at full speed," noting that the attacker was capitalizing on the remaining liquidity before the market fully reacted.
- Extreme Depeg and Liquidity Drain: The market reaction was brutal. D2 Finance reported that USR was observed selling for as low as 50 cents on certain trades, indicating a severe loss of confidence and worsening liquidity across various decentralized exchanges. On Curve Finance, one of USR’s most liquid pools with a 24-hour volume of $3.6 million, the stablecoin flash-crashed to an astonishing low of 2.5 cents against USDC. This extreme depeg occurred just 17 minutes after the initial 50 million tokens were minted, underscoring the instantaneous and devastating nature of such exploits. The frantic attempts by legitimate holders to sell their USR were visible on-chain through "multiple failed transactions," signaling the rapidly diminishing liquidity and escalating panic.
- Estimated Financial Damage: Amidst the market chaos, D2 Finance estimated that the attacker successfully extracted approximately $25 million from the attack. This figure represents the value the attacker was able to realize by selling the illicitly minted USR before its value completely collapsed.
- Current Status: As of the latest reports, Resolv USR has shown a partial recovery from its lowest point but remains significantly depegged. CoinGecko data indicates USR trading around 87 cents, still approximately 13% off its intended $1 peg. The Curve pool, while recovering from its 2.5-cent low, was trading around 84.5 cents, reflecting the severe damage to market confidence and liquidity.
Technical Analysis of the Vulnerability
The precise technical flaw that enabled the exploit is under active investigation, but preliminary analyses from security experts and on-chain observers offer several possibilities. D2 Finance specifically highlighted that the "minting function on USR’s contract was somehow broken." They posited three primary potential vectors for the attack:
- Oracle Manipulation: Many stablecoins rely on external data feeds, known as oracles, to provide real-world price information. If an attacker could manipulate the oracle to report a false price for the collateral (e.g., making it appear that a small amount of USDC was worth a vast sum of USR), they could trick the contract into minting an excessive number of tokens. This is a common attack vector in DeFi.
- Compromised Off-Chain Signer: Some protocols, particularly those involving centralized components or hybrid models, might use an off-chain signer (a private key held by the project team or a trusted entity) to authorize certain operations, such as minting or pausing functions. If this private key were compromised (e.g., through a phishing attack, brute force, or insider threat), the attacker could gain unauthorized control over the minting process.
- Missing Amount Validation: This refers to a flaw within the smart contract code itself, where the logic for validating the amount of collateral deposited against the amount of stablecoin minted is either incorrect or entirely absent. A bug in this validation could allow an attacker to deposit a minimal amount of collateral but request and receive a vastly larger quantity of new tokens, as appears to have happened with the $100,000 USDC deposit yielding 50 million USR. This would represent a critical smart contract vulnerability.
The sheer volume of unbacked tokens minted suggests a fundamental flaw in the core minting logic, regardless of whether an oracle was gamed or a signer was compromised. The absence of proper validation would be a severe oversight in smart contract development, particularly for a stablecoin designed to maintain a fixed value.
Official Response and the Path to Recovery
Resolv Labs’ immediate response to pause all protocol functions was a critical, albeit drastic, step. This action prevents the attacker from further exploiting the vulnerability and protects remaining assets within the protocol. However, it also means that users cannot interact with their USR tokens or other associated services within the Resolv ecosystem, leading to immediate liquidity issues and potential panic among holders.

The team’s statement that they are "actively working on recovery" implies a multi-faceted approach. This typically involves:
- Forensic Investigation: A thorough audit of the compromised smart contract and associated systems to pinpoint the exact vulnerability and how it was exploited. This often involves engaging external blockchain security firms.
- Communication with Law Enforcement: Given the significant financial loss, Resolv Labs is likely to contact relevant law enforcement agencies and blockchain analytics firms to trace the stolen funds, though the decentralized nature of crypto often makes recovery challenging.
- Community Updates: Regular and transparent communication with the affected community is vital to rebuild trust and manage expectations regarding recovery efforts, potential compensation, or a migration plan.
- Mitigation and Patching: Once the vulnerability is identified, a patch or upgrade to the smart contract will be necessary, often requiring a new deployment and potentially a token swap for existing holders.
- Compensation or Recovery Plan: For affected users, the most pressing concern is the recovery of their lost funds. Resolv Labs may explore various options, such as using treasury funds, seeking external investment, or implementing a token buyback program, though such plans are often complex and depend on the project’s financial health and strategic decisions.
Broader Implications for DeFi and Stablecoins
The Resolv USR exploit, while a significant event for its community, carries broader implications for the entire DeFi ecosystem and the future of stablecoins.
- Renewed Scrutiny on Smart Contract Security: The incident serves as a potent reminder that despite advances in blockchain security, smart contract vulnerabilities remain a persistent threat. It underscores the absolute necessity of rigorous, multi-layered security audits by reputable third-party firms, ongoing bug bounty programs, and formal verification methods for all DeFi protocols, especially those handling significant user funds or maintaining critical functions like stablecoin minting. The fact that such a fundamental flaw could exist highlights the need for continuous vigilance.
- Trust and Confidence in Newer Stablecoins: While established fiat-backed stablecoins like USDC and USDT have robust auditing and reserve management, newer or smaller stablecoin projects, particularly those employing more complex algorithmic or crypto-backed mechanisms, face greater scrutiny after incidents like this. Investors and users may become more wary of stablecoins without a long track record of stability and transparent, verifiable collateral. This could lead to a flight to quality, favoring battle-tested stablecoins.
- Regulatory Pressure: Crypto exploits, especially those involving stablecoins, inevitably attract the attention of financial regulators worldwide. Incidents of large-scale fund loss due to protocol vulnerabilities strengthen arguments for increased regulatory oversight, consumer protection measures, and clear accountability frameworks within the DeFi space. Regulators are likely to point to such events as evidence of systemic risk.
- The "DeFi Hack Cycle": The exploit comes after a period where crypto-related hacks saw a sharp decline in February, with $49 million lost compared to $385 million in January. However, this decline was largely attributed to attackers shifting towards phishing scams rather than complex protocol exploits. The Resolv USR incident demonstrates that sophisticated protocol exploits are far from eradicated and remain a potent threat, reminding the industry that security is an ongoing battle, not a solved problem.
- Risk for the Entire Ecosystem: The depeg of a stablecoin, even a relatively smaller one, can have cascading effects. Stablecoins are often used as collateral in lending protocols, liquidity in decentralized exchanges, and a base asset for various yield-farming strategies. A sudden depeg can trigger liquidations, disrupt trading pairs, and cause significant losses for users across interconnected DeFi protocols, creating systemic risk.
Lessons Learned and Moving Forward
The Resolv USR depeg is a painful lesson, reiterating the critical importance of security and resilience in the fast-evolving world of decentralized finance. For projects, it emphasizes the need for:
- Comprehensive Audits: Not just one, but multiple audits from different reputable firms, focusing on core logic, economic viability, and potential attack vectors.
- Robust Risk Management: Implementing circuit breakers, multi-signature controls, and decentralized governance mechanisms that can react swiftly to unforeseen events.
- Transparency: Clear and honest communication with users, especially during crises, is paramount for maintaining any semblance of trust.
For users, the incident is a stark reminder to:
- Do Your Own Research (DYOR): Thoroughly investigate the security, audit history, and backing mechanisms of any stablecoin or DeFi protocol before committing funds.
- Understand the Risks: Be aware that even stablecoins are not immune to risks, including smart contract exploits, oracle manipulation, and operational failures.
- Diversify: Avoid concentrating significant funds in single, unproven protocols or stablecoins.
As Resolv Labs grapples with the aftermath, the crypto community watches closely. The success or failure of their recovery efforts will not only determine the future of their project but will also offer valuable insights into how the broader DeFi ecosystem can evolve to better protect users from increasingly sophisticated threats. The incident underscores that while innovation in DeFi promises financial liberation, it must be meticulously balanced with an unwavering commitment to security and user protection.